Home > Blog > Industry playbook > dApp Security audit checklist: Essential technical review points
dApp Security audit checklist: Essential technical review points
By Borislav Itskov
Oct 21, 2025 • 8 min read
Let's be honest: launching a dApp without a proper security audit is like leaving your front door wide open in a neighborhood full of hackers. With critical security vulnerabilities found in the majority of Web3 projects and billions lost to exploits each year, a comprehensive security review isn't just recommended - it's survival.
Whether you're a founder preparing for launch, an investor doing due diligence, or a developer who wants to sleep soundly at night, this checklist covers everything you need to know about dApp security audits.
Why dApp security audits matter
The numbers don't lie: Web3 security breaches cost the industry $2.2 billion in 2024 alone, with over 300 individual hacking incidents. From major exchange exploits to countless smaller attacks that barely make headlines, the pattern is clear - security isn't optional in Web3.
Here's what makes dApp security particularly challenging: Smart contract immutability creates unique challenges. While upgradeable contracts and emergency mechanisms exist, they come with trade-offs. The real issue isn't that you can't update code - it's that attackers won't wait for you to react. When someone discovers a vulnerability, they'll exploit it immediately.
High-value targets. dApps often handle significant amounts of cryptocurrency, making them attractive targets for sophisticated attackers.
Complex attack surfaces. Modern dApps involve smart contracts, frontend interfaces, backend APIs, and third-party integrations - each presenting potential vulnerabilities.
Regulatory scrutiny. As Web3 matures, regulators are paying closer attention to security practices. A major breach doesn't just cost money - it can trigger compliance issues.
The good news? Most vulnerabilities are preventable with proper auditing. A thorough security review before launch can save you millions in potential losses and protect your reputation in the long run. Our Web3 technical auditing services help identify vulnerabilities before they become exploits.
Pre-audit preparation checklist
Before diving into the technical review, proper preparation sets the foundation for an effective audit. Here's what you need to have ready:
Documentation requirements:
- Complete technical documentation of all smart contracts
- Architecture diagrams showing system interactions
- User flow documentation for all critical paths
- API documentation for off-chain components
- Deployment and upgrade procedures
Code repository setup:
- Clean, well-organized codebase with clear commit history
- All dependencies clearly documented and up-to-date
- Separate branches for different deployment environments
- Comprehensive README with setup instructions
Testing environment:
- Deployed test instances on relevant networks
- Test data and scenarios that cover edge cases
- Access credentials for auditors (with appropriate permissions)
- Monitoring and logging systems in place
Scope definition:
- Clear boundaries of what's included in the audit
- Priority levels for different components
- Timeline and milestone expectations
- Communication protocols with the audit team
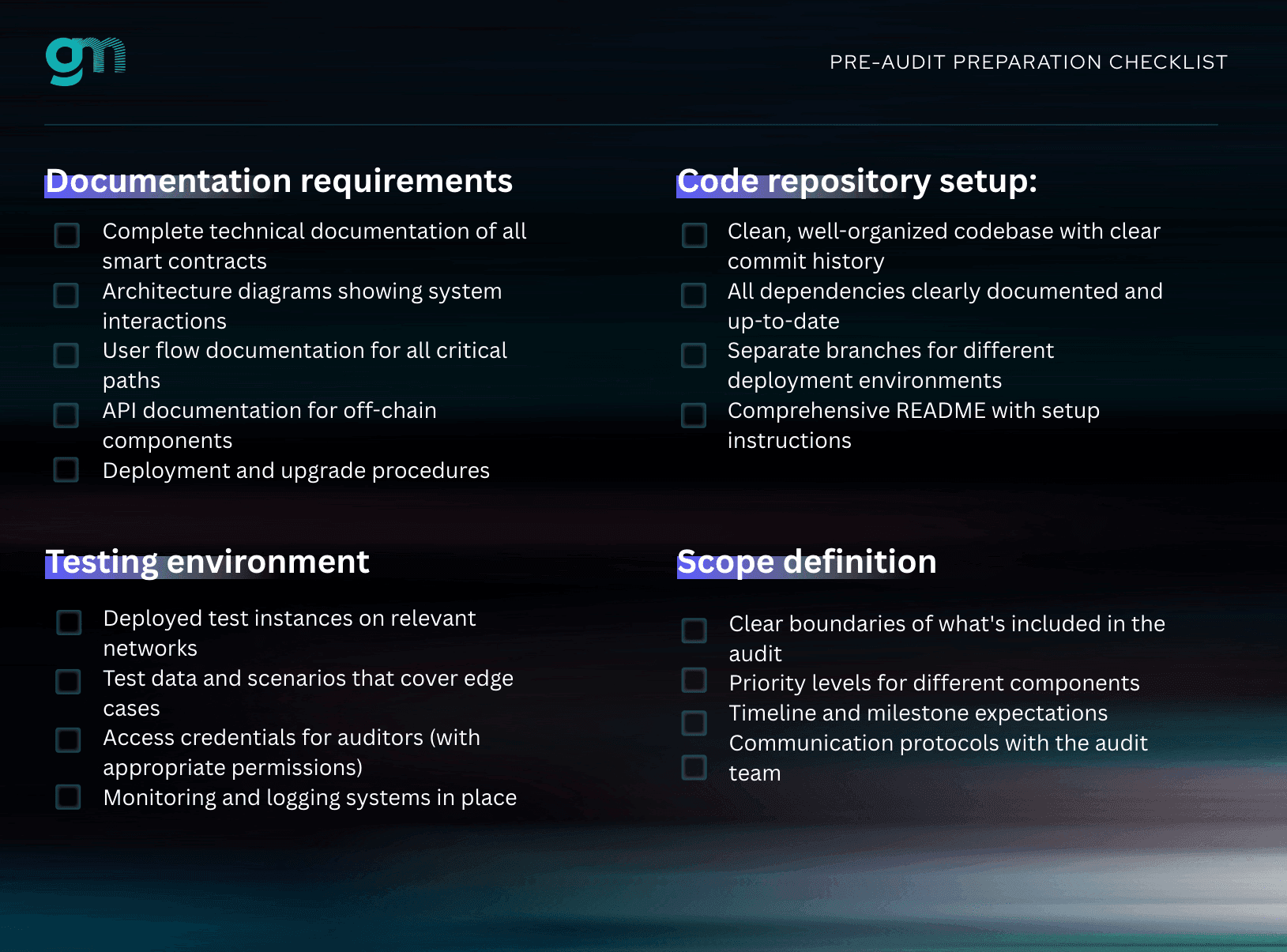
Getting these basics right upfront saves time, reduces costs, and ensures the audit team can focus on finding real vulnerabilities instead of figuring out how your system works.
Core technical review areas
A comprehensive dApp security audit covers multiple layers of your application stack. Here's what should be examined in each area:
Smart contract security assessment
The heart of any dApp audit focuses on the smart contracts themselves. Key areas to examine include:
Code quality and best practices:
- Use of established frameworks (OpenZeppelin, etc.)
- Proper error handling and input validation
- Gas optimization and efficiency
- Code readability and documentation
Common vulnerability patterns:
- Reentrancy attacks and state manipulation
- Integer overflow/underflow issues
- Access control and permission management
- Oracle manipulation and external data validation
Business logic verification:
- Contract functions match intended behavior
- Edge cases and boundary conditions
- Mathematical operations and token calculations
- Upgrade mechanisms and governance controls
Frontend security review
The user-facing layer often gets overlooked, but it's equally critical:
Wallet integration security:
- Proper transaction signing workflows
- Secure handling of private keys and seeds
- Protection against phishing and social engineering
Data handling:
- Input sanitization and validation
- Secure API communication
- Protection of sensitive user information
Backend infrastructure audit
For dApps with off-chain components:
API security:
- Authentication and authorization mechanisms
- Rate limiting and DDoS protection
- Data encryption in transit and at rest
Database security:
- Access controls and user permissions
- Backup and recovery procedures
- Protection against injection attacks
Third-party integration analysis
Modern dApps rarely exist in isolation. They integrate with external protocols, oracles, and services that can introduce vulnerabilities. Here's what should be examined:
External contract interactions:
- Security of integrated protocols
- Proper handling of external calls
- Fallback mechanisms for service failures
Oracle and data feed security:
- Price manipulation resistance
- Multiple data source validation
- Circuit breakers for anomalous data
The complete dApp security audit checklist
Here's your comprehensive checklist for conducting a thorough dApp security audit:
Smart contract fundamentals
- Critical: All functions have proper access controls
- Critical: Reentrancy protection implemented where needed
- Critical: Integer overflow/underflow protection in place
- High: Input validation on all external functions
- High: Proper error handling and revert conditions
- Medium: Gas optimization for expensive operations
- Medium: Events emitted for all state changes
- Low: Code documentation and comments
Business logic verification
- Critical: Token transfer logic is mathematically sound
- Critical: Voting/governance mechanisms can't be manipulated
- High: Edge cases handled appropriately
- High: State transitions follow expected patterns
- Medium: Fee calculations are accurate
- Medium: Time-based logic accounts for block time variations
Security mechanisms
- Critical: Multi-signature requirements for admin functions
- Critical: Emergency pause/stop mechanisms
- High: Rate limiting on sensitive operations
- High: Slippage protection for DEX interactions
- Medium: Circuit breakers for unusual activity
- Medium: Monitoring and alerting systems
External integrations
- Critical: Oracle price feeds have manipulation protection
- Critical: External contract calls handle failures gracefully
- High: Third-party dependencies are up-to-date and secure
- High: Cross-chain bridge interactions are validated
- Medium: API endpoints have proper authentication
Frontend security
- High: Wallet connection flows are secure
- High: Transaction data is properly validated before signing
- Medium: User inputs are sanitized
- Medium: Sensitive data is not exposed in client-side code
Common dApp vulnerabilities to watch for
Here are some common vulnerabilities that appear often in dApp security audits:
Reentrancy attacks (Critical): The classic Web3 vulnerability where external calls can manipulate contract state. Always use checks-effects-interactions pattern and consider reentrancy guards.
Access control issues (Critical): Misconfigured permissions that allow unauthorized users to call admin functions. Implement role-based access control and regularly review permissions.
Frontrunning vulnerabilities (High): A system working perfectly fine until a bot discovers how to front run transactions and make them invalid in the process. Sometimes it could be as simple as changing a flag, or calling a cancel function. Mitigation: Use commit-reveal schemes and implement time delays for sensitive operations.
Gas griefing attacks (Medium): Attackers who deliberately cause transactions to fail by manipulating gas usage. Set appropriate gas limits and implement fallback mechanisms.
Cross-chain bridge vulnerabilities (Critical): With the multi-chain explosion, bridge exploits have become the new frontier for attackers. Validate cross-chain message authenticity, implement proper slashing mechanisms, and never trust external chain data without verification.
Oracle manipulation (Critical): Price oracle attacks that manipulate external data feeds to exploit your protocol. Use multiple oracle sources, implement price deviation checks, and add time-weighted average prices (TWAP) for critical operations.
Governance attacks (High): Flash loan governance attacks where attackers temporarily acquire voting power to pass malicious proposals. Implement voting delays, require minimum holding periods, and use timelocks for critical changes.
Slippage and sandwich attacks (Medium): Bots that manipulate AMM prices around user transactions. Implement proper slippage protection, use commit-reveal for large trades, and consider batch auction mechanisms.
The key is understanding that security isn't just about preventing attacks - it's about building systems that fail gracefully and protect user funds even when things go wrong.
Post-audit recommendations and monitoring
A security audit is just the beginning, not the end, of your security journey. Here's how to maintain security after launch:
Ongoing monitoring:
- Set up on-chain monitoring for unusual activity
- Implement real-time alerts for large transactions
- Monitor gas usage patterns for anomalies
- Track smart contract interactions and state changes
Regular security reviews:
- Schedule periodic re-audits, especially after major updates
- Review and update security procedures quarterly
- Stay current with new vulnerability patterns and attack vectors
- Maintain relationships with security researchers and white-hat hackers
Incident response planning:
- Develop clear procedures for security incidents
- Establish communication channels for emergency situations
- Practice incident response with tabletop exercises
- Maintain emergency contacts for key stakeholders
Remember: in Web3, security is never "done." The threat landscape evolves constantly, and your security practices need to evolve with it.
Ready to secure your dApp?
At goodmorning, we combine deep technical expertise with real-world Web3 experience to help you build with confidence. From comprehensive security audits to ongoing monitoring, we're here to make sure your project is built to last.
Book a free consultation with our team and let's make sure your Web3 project is ready for whatever the blockchain throws at it.
Because in Web3, you don't get second chances. Make every security decision count - with goodmorning on your side.

Written by Borislav Itskov
Software engineer with 10+ years of experience. Self-made, bottom-to-top kind of guy - started out building tiny Joomla projects over a decade ago and worked my way up to Ethereum-based products, most notably Ambire Wallet. Co-author of ERC-5792, the standard aimed at making Ethereum UX great. Introduced Schnorr signatures to the Ethereum account abstraction ecosystem after winning an Ethereum Foundation grant and building a Schnorr multisig² library to demonstrate the approach. Hackathon winner at Prague 2023. Sound-money believer.
Ready to take the next step in your Web3 journey?
Drop us a message and let's see what Web3 development services we can do for you.